Coverware: Ransomware Demands continue to rise as Data Exfiltration becomes common, and Maze subdues
The Coveware Quarterly Ransomware Report describes ransomware incident response trends during Q3 of 2020. Ransomware groups continue to leverage data exfiltration as a tactic, though trust that stolen data will be deleted is eroding as defaults become more frequent when exfiltrated data is made public despite the victim paying. In Q3, Coveware saw the Maze group sunset their operations as the active affiliates migrated to Egregor (a fork of Maze). We also saw the return of the original Ryuk group, which has been dormant since the end of Q1.
Average Ransomware Increases as Attackers Target Bigger Companies
Average Ransom Payment
+31% from Q2 2020
Median Ransom Payment
+2% from Q2 2020
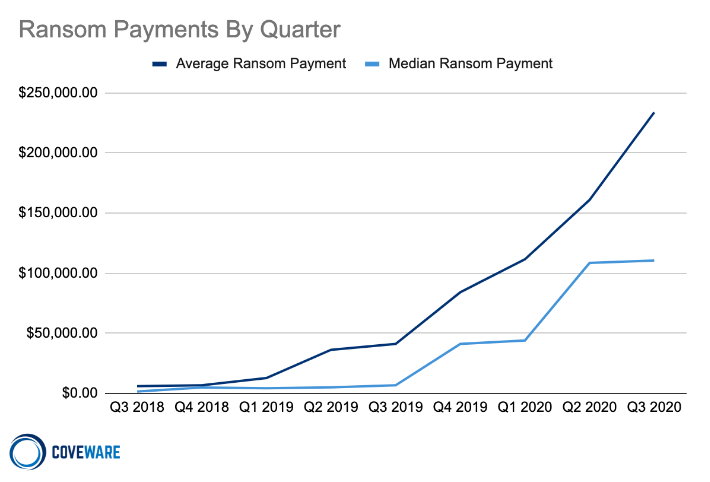
Average and Median Ransom Payments
The average ransom payment increased to $233,817 in Q3 of 2020, up 31% from Q2. The median payment in Q3 rose slightly from $108,597 to $110,532, reflecting how large, big game payments continue to drag the averages up. The disequilibrium within the cyber extortion industry was evident when attackers discovered that the same tactics, techniques, and procedures (TTPs) that work on a 500 person company can work on a 50,000 person company and the potential payoff is substantially higher. The dramatic increase in ransom amounts may imply a higher degree of sophistication as attackers go upmarket, but Coveware does not believe that the attacks are more sophisticated.
The biggest change over the past 6 quarters is threat actors now realize that their tactics scale to much larger enterprises without much of an increase in their own operating costs. The profit margins are extremely high and the risk is low. This problem will continue to get worse until pressure is applied to the unit economics of this illicit industry. It is also possible that the influx of remote and work-from-home setups using RDP and other remote technologies allowed threat actors to leverage attack vectors that previously didn’t exist.
DopplePaymer, Conti, Wasted, Nephilim and Avvadon make it to the Top 10, Egregor inherits Maze
| Rank | Ransomware Type | Market Share % | Change in Ranking from Q2 2020 |
|---|---|---|---|
| 1 | Sodinokibi | 16.2% | - |
| 2 | Maze | 13.6% | - |
| 3 | Netwalker | 9.9% | +1 |
| 4 | Phobos | 5.0% | -2 |
| 5 | DopplePaymer | 4.3% | New in Top 10 |
| 6 | Snatch | 4.0% | +2 |
| 6 | Conti | 4.0% | New in Top 10 |
| 8 | Lockbit | 3.6% | +1 |
| 9 | Dharma | 2.3% | -4 |
| 10 | Nephilim | 2.0% | New in Top 10 |
| 10 | Avaddon | 2.0% | New in Top 10 |
Top 10: Market Share of the Ransomware attacks
The third quarter marked both the peak and the end of Maze ransomware. Based on our tracking of Maze activity, their last enterprise attacks occurred in late September, and they have since announced they are sunsetting. Since then, less senior affiliates, the ‘young and daring’, have likely forked the Maze ransomware code into the Sekhmet and Egregor ransomware variants. Judging by their prolific rise and similar tactics, Egregor seems to be the heir apparent.
Read the full article: https://www.coveware.com/blog/q3-2020-ransomware-marketplace-report
